October 2023 Update: Intezer now analyzes URLs, including detecting QR codes, that we collect as evidence for automated alert triage and phishing investigations.
As part of our ongoing effort to allow you to investigate any security incident, we have made an important expansion to the types of artifacts Intezer can help you with. We are very excited to announce the latest addition to Intezer: URL analysis. This release includes a public API, allowing you to integrate Intezer within your organizations’ phishing investigation pipelines.
The ability to quickly and effectively understand whether a certain URL poses a threat is valuable for many use cases: URLs are extremely common artifacts in suspicious emails and SOC alerts. They are frequently encountered during incident response and malware analysis. Modern cyber attacks typically involve the use of URLs in one or more ways:
- Credential harvesting links (phishing) – Links that lead to fake websites masquerading as a legitimate service in an attempt to trick the user to type their private credentials and steal them. Typically used in phishing emails.
- C&C address – For communication with the malware operators. Malware often communicates via HTTP(s) with its C&C server in order to receive and send data.
- Malware drop sites – For downloading malware payloads. Malware droppers (e.g. a malicious PDF attachment) may use common file hosting services (e.g. Google Drive) in order to download malicious payloads while evading URL reputation-based filtering.
- Browser exploitation – Where a victim browses into a compromised website that will exploit a vulnerability in his browser in order to give the attacker control over the victim’s machine. Often used by exploit kits.
How Do We Tackle URL Scanning?
Our goal was to build a comprehensive solution that provides reliable answers for the most relevant questions when you are analyzing URLs:
- Is this URL a threat?
- If so, why and what kind of threat?
- What does the webpage look like?
- Does it download a file? What is that file?
It was important for us to provide you with fast, accurate, and easy to interpret scan results, allowing you to focus on real incidents. Additionally, we designed our solution to be useful for analysts of all skill levels.
To achieve that, we have decided to go for a best-of-all-worlds approach. We combined Intezer’s proprietary, unique scan insights with the best-of-breed existing solutions for URL analysis (urlscan.io and apivoid.com), each with a distinct approach. We tied everything together in a clean interface that makes our results straightforward and simple for analysts at all skill levels. On the analysis page you will find:
- APIvoid score
- A clear screenshot of the URL’s response page
- Network redirection chain
- Domain information
- URL analysis indicators breakdown divided into 3 categories: malicious, suspicious and informative
- Detected brand name used for the phishing lure (for credential harvesting URLs)
- Dropped file verdict and family (for malware drop URLs)
Using our URL analysis API to automate the whole process, teams can build a phishing pipeline that analyzes URLs and dropped files.
Some URL Analysis Examples
One very common and familiar scenario is receiving email that contains a link to a login page of some online service. In the example below we can see an analysis of a link that appeared in an email that was supposedly sent from Amazon:

After analysis we can clearly see it is actually a malicious phishing site masquerading as an Amazon login page, most likely in an attempt to harvest the login credentials from the user.
Another common scenario is dealing with download links. Of course, you can go through the process of downloading the file yourself and analyzing it separately. Not only is it a hassle but it is also risky. With the new URL analysis feature you can simply paste the URL and we will analyze both the URL and any file that is downloaded.
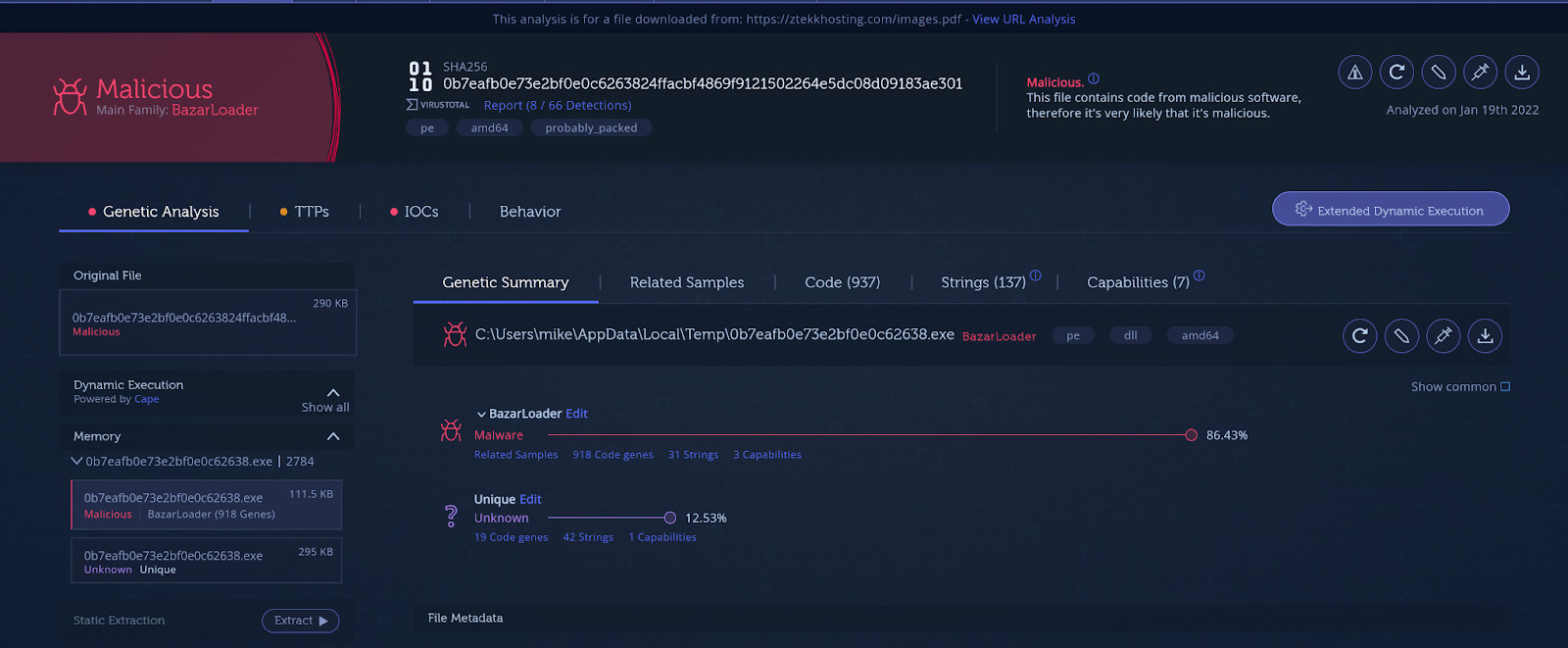
In the example below, you can see an analysis for a download link to a PDF file, one of the most frequently used malicious email attachments.
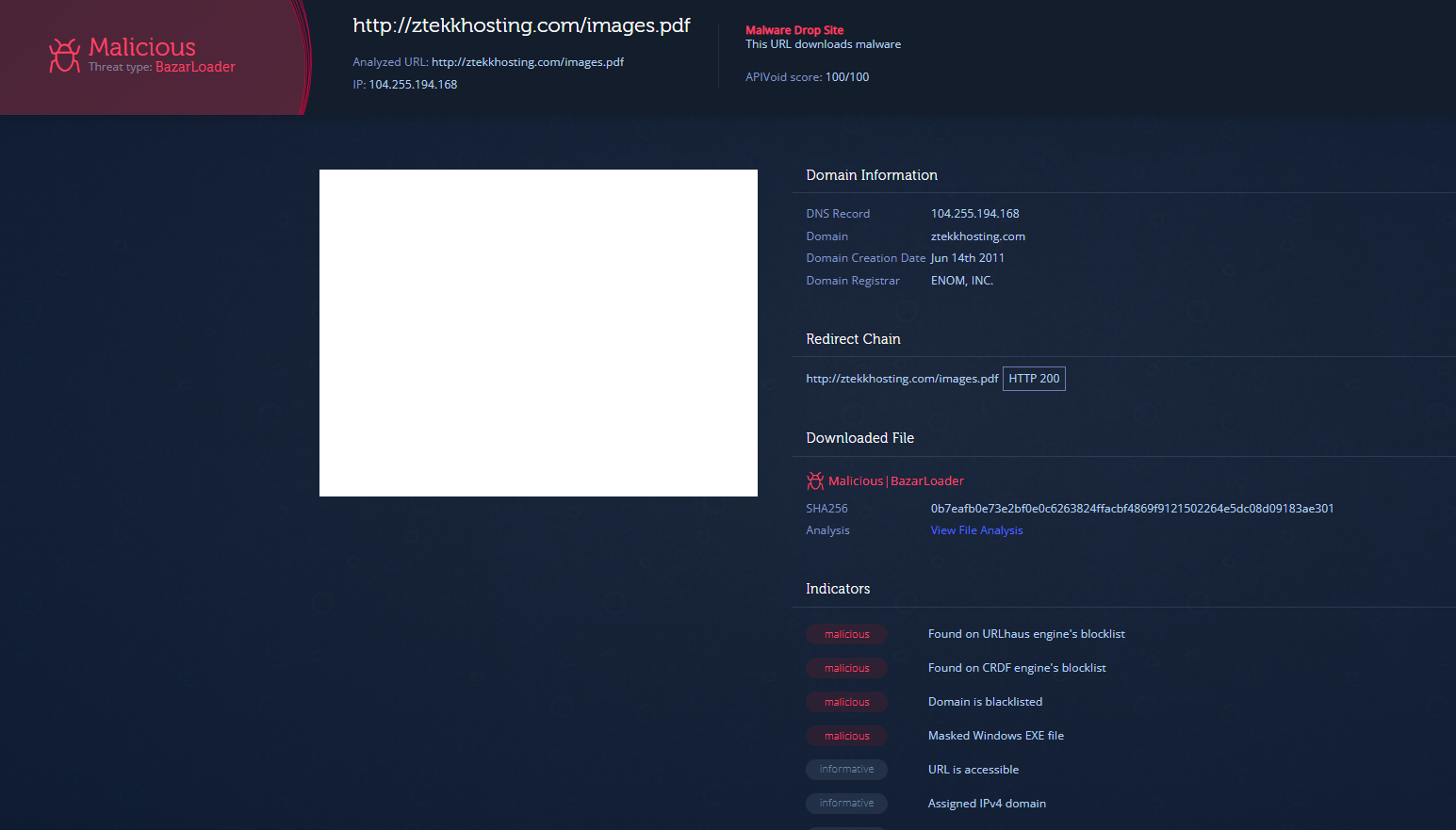
We can see the URL is malicious and specifically a malware drop site. Viewing the analysis of the downloaded file (which is linked to from the URL analysis results) it becomes clear that it is a dropper for the BazarLoader malware.
Start Accelerating URL Scanning With Intezer
Try it now using our public API or with your Intezer account!