The modern SOC needs more than AI alone can offer. Intezer pairs AI flexibility with deterministic, forensic guardrails, along with on-demand expert access, and predictable, endpoint-based pricing, so security teams can scale without compromise.
Intezer AI SOC investigates every alert at forensic depth so your team can focus on real threats, while investigation outcomes continuously improve detection coverage.
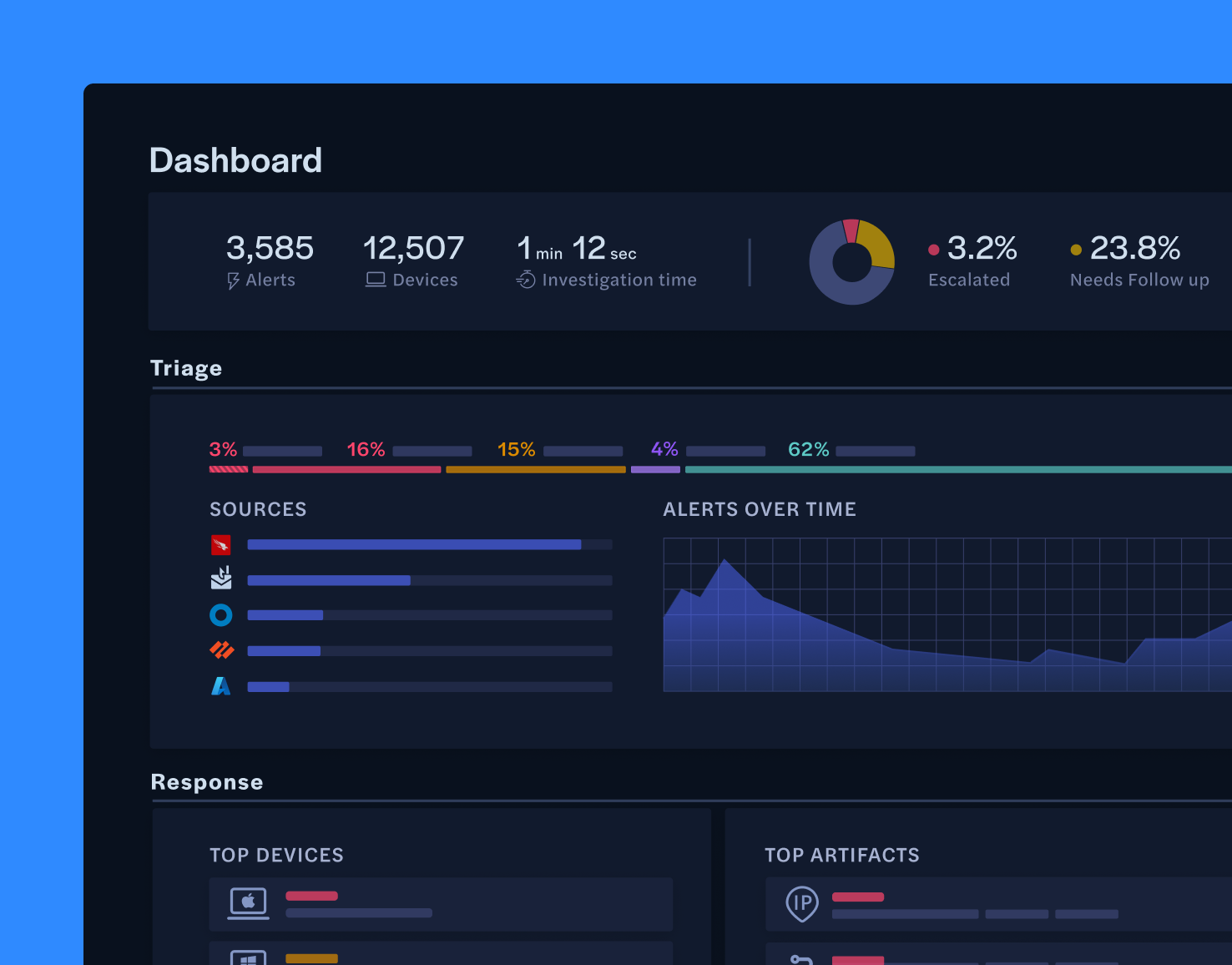
Intezer AI SOC combines proven forensic capabilities, including endpoint forensics, reverse engineering, network artifact analysis, and sandboxing, with agentic AI reasoning. The result is sub-minute triage across 100% of alerts, with fewer than 2% escalated and 98% verdict accuracy, all with full transparency.
Integrate with CrowdStrike, SentinelOne, and Microsoft Defender in seconds.
Intezer automatically collects and analyzes files, logs, command lines, memory images, and more to resolve false positives and escalate real threats with recommended actions for review or automated remediation.
Accurately triage Entra ID and Okta alerts to reduce MTTR.
Intezer queries IDP data, reviews findings against threat intelligence, contacts users for feedback, as well as proposes and executes the next steps.

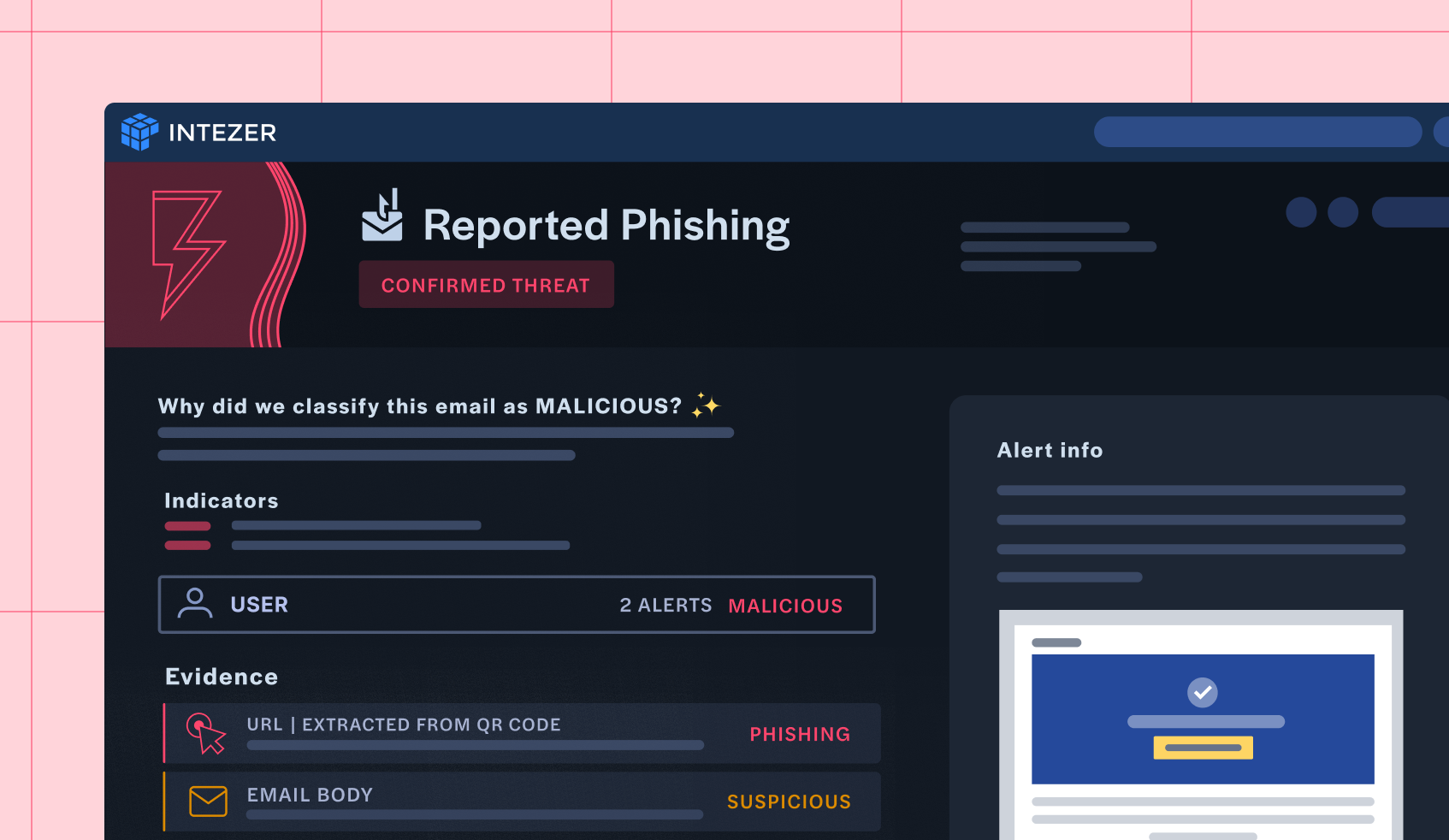
Eliminate manual review of abuse mailboxes.
Intezer connects to Office 365, Proofpoint and similar tools to handle triage automatically.
It parses raw email data, scans attachments, and analyzes URLs to detect common phishing tactics and return a clear verdict with priority, classification, and context. Only the alerts that need a human actually reach one.
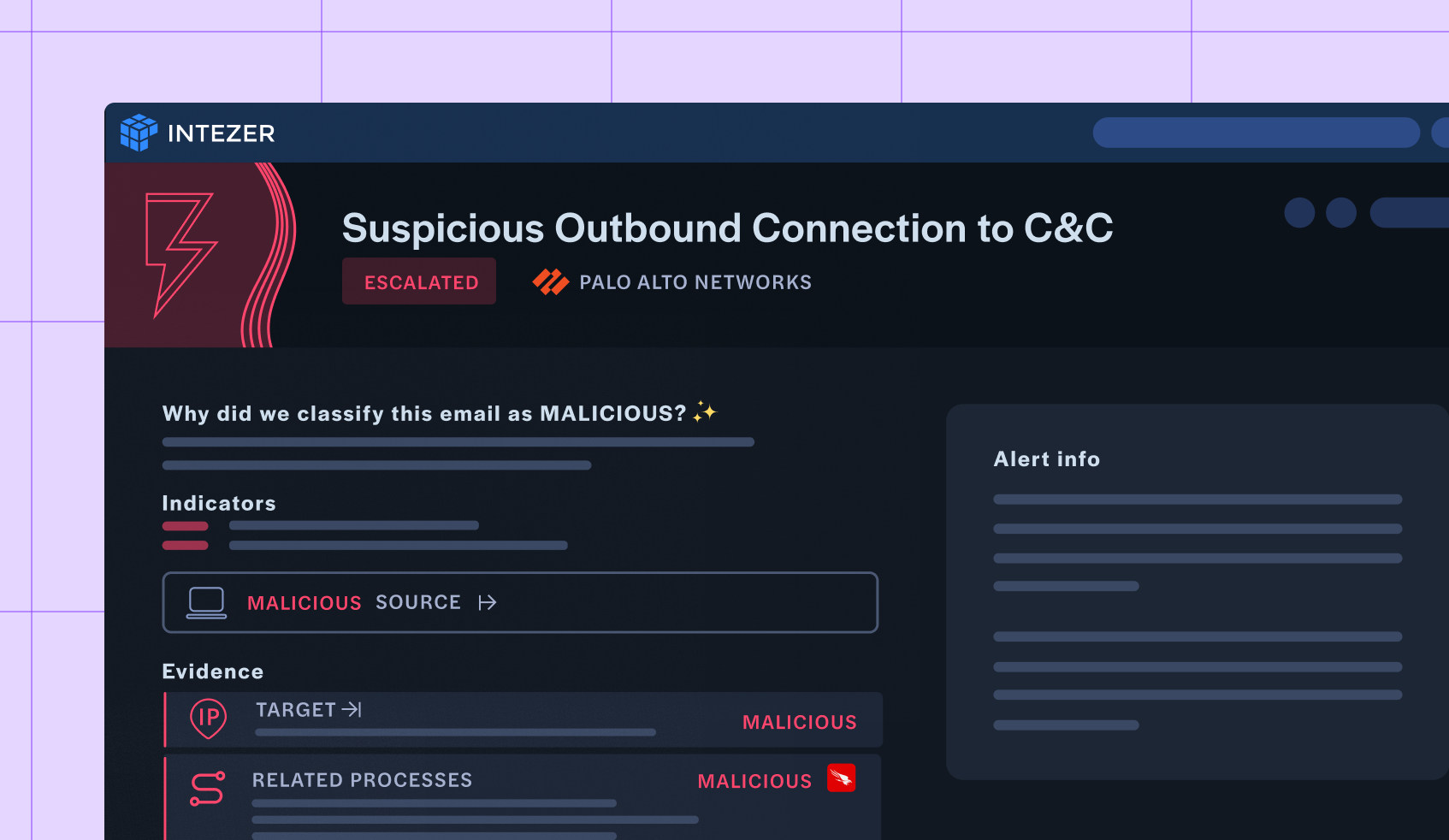
Seamlessly connect into your entire security stack and network.
Intezer deeply analyzes IPs, URLs, correlates alerts to identify patterns, reviews environment context and take action, resolving false positives, auto-remediating where relevant and escalating real threats.
Keep your cloud assets secure with deep integrations into your SIEM, workload protection solutions, or tools like Wiz.
Investigate alerts with full context from logs and connected data sources. Perform in-depth analysis to understand the scope of any threat. Get detailed recommendations on remediation steps and automatically resolve false positives.
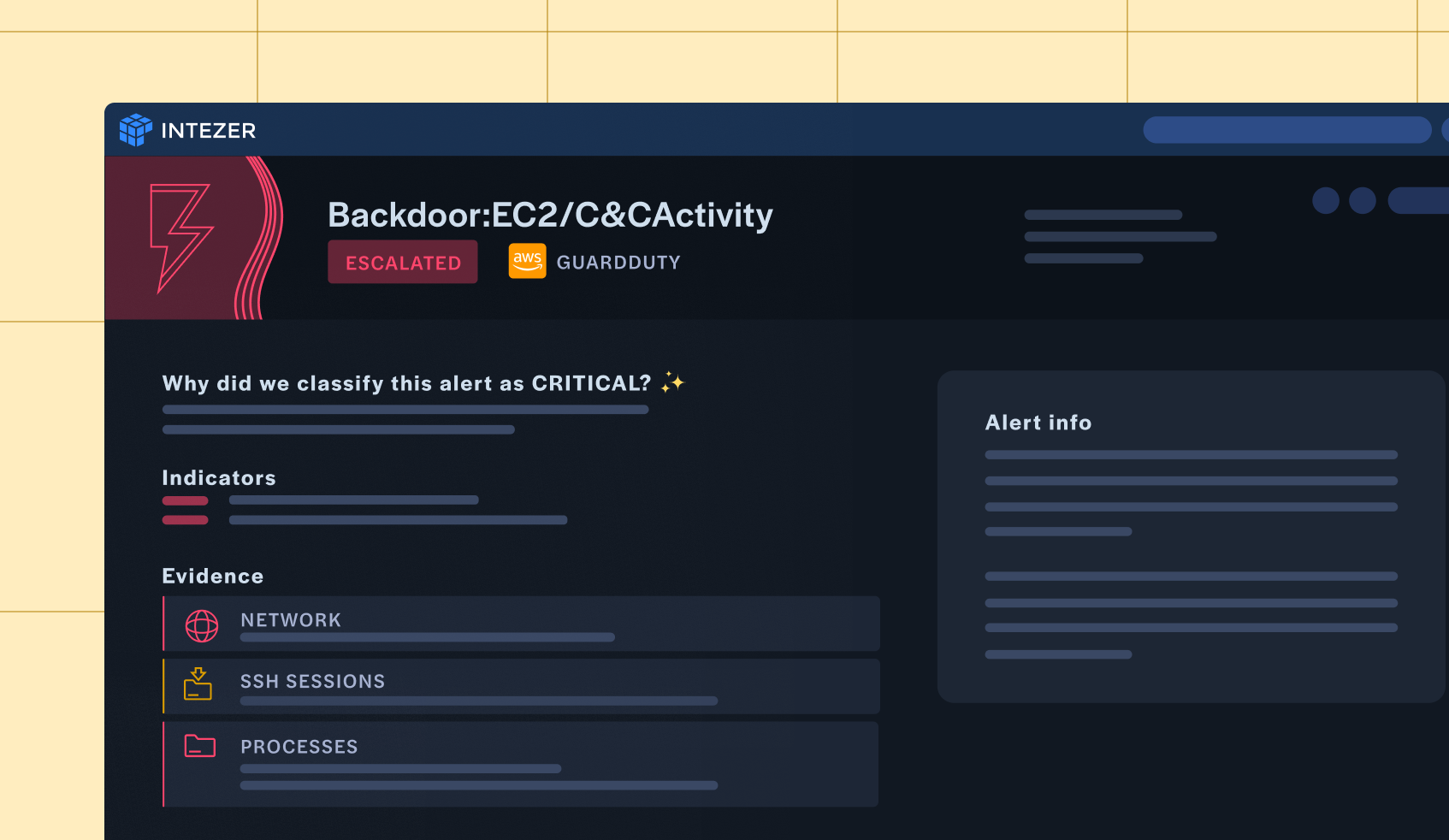
Intezer AI SOC combines multiple AI models, both proprietary and commercial, with deterministic methods such as endpoint forensics, reverse engineering, network artifact forensics, sandboxing, static analysis and more. Together, this approach mirrors the triage process that expert, human analysts follow, maintaining high accuracy at unmatched speed and scale.

Our native integrations are built for the depth and rigor of the triage and forensic investigation process, providing robust, full-featured connections between tools. This allows Intezer to ingest alerts from all major sources within seconds, gather richer evidence, and deliver deeper context in every analysis. Remediation actions can be easily automated with explicit human approval.
The modern SOC needs more than AI alone can offer. Intezer pairs AI flexibility with deterministic, forensic guardrails, along with on-demand expert access, and predictable, endpoint-based pricing, so security teams can scale without compromise.
Regardless of alert volume, Intezer delivers consistent, lightning fast and in-depth triage and investigation. Every alert, including low-severity ones, receives the same rigorous level of scrutiny, reducing unnecessary escalations and ensuring your team catches threats that human-only teams will miss.
Intezer AI SOC incorporates advanced forensic capabilities, from automated evidence collection via EDR/SIEM/IDP to memory analysis, reverse engineering, network artifact forensics, and sandboxing. This enables sub-minute, scalable triage for every alert, including low-severity events often abused by attackers. You get deep investigation at unprecedented speed and volume.
With transparent triage logic, clear explanations, and the ability for analysts to review or override escalated alerts, Intezer keeps humans in the loop. Intezer AI SOC continuously improves through user feedback and in-house QA with ongoing self-testing and benchmarking. Combined with 24/7 access to our expert analysts, Intezer is a genuine security partner.
Intezer’s unique architecture combines deterministic analysis with efficient AI models to triage most alerts without resource-intensive LLM processing. This delivers native scalability and stable, predictable pricing tied to organizational size, such as number of endpoints, so you get enterprise-grade performance without unpredictable cost spikes.
Sandro Ramirez
Head of Security, Cotemar
Jim Radzicki
President
Christian Hellemar
Head of Cybersecurity Services, tech stn.
Todd Willoughby
Director
Intezer thoroughly investigates every alert in minutes. Instead of “accepting” the risk hidden in your unreviewed low-severity alerts, you can rest easier knowing that every alert will be fully analyzed, every time.
With fewer escalations and higher accuracy, SOC managers can refine their resource allocation by reviewing their MDR contract or increasing endpoints under management without increasing their team.
With Intezer taking on primary triage duties, your team can now tackle more strategic security initiatives, driving meaningful impact to your security posture.
Intezer leverages a combination of proprietary and commercial AI models, along with proven forensic tools for crafting the bottom-line incident triage assessments. In addition, users can fine-tune Intezer’s decision making process to their own organization and policies.
Intezer can ingest and triage alerts from endpoint security products, SIEM tools and user-reported phishing pipelines. Intezer can also integrate with tools for ticketing and case management, such as ServiceNow or SOAR tools.
Some of our most popular integrations are for CrowdStrike, SentinelOne and Microsoft Defender to automate endpoint security alert triage and response.
Intezer can also be interacted with and perform automated security operation tasks through our RESTful API and Python SDK.
Check out our full Integration list here.
Intezer’s AI-driven technology functions as an extension of your team to help you further reduce your SOC/IR workload, often working side-by-side with your existing security stack.
The primary onboarding tasks are connecting your alert sources and then adding members of your team as new users to your Intezer account.
It takes a few minutes to connect a security tool as a new alert source in Intezer, using an API key with the necessary permissions. After adding your API key to Intezer, you should start seeing alert triage results in your dashboard within the hour. If you want to know more about getting started with Intezer, you can book a demo to talk with us about integrating Intezer into your tech stack and team’s processes.
Top brands like Equifax, MGM Resorts, NVIDIA and other Fortune 500 enterprise security teams use Intezer to triage and investigate the high volume of alerts they receive daily.
To find out how other companies are using Intezer’s AI-powered platform, check out our case studies here.
Discover how AI-powered endpoint triage can eliminate alert fatigue and supercharge your SOC’s efficiency.