AI SOC for Enterprise
Trusted by over 150 of the world's most targeted enterprises



The SOC model is broken
Whether operated in-house or through an MDR, unacceptable risk tolerance has become reality for most SOCs.
Your SOC. Zero constraints.
Where human SOC teams review outcomes, not tickets
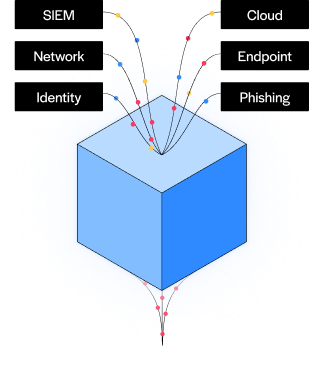
100% of alerts investigated at forensic depth

Detection rules automatically tuned
Sub-minute triage, 98% verdict accuracy
Fewer than 2% of alerts are escalated for human review so teams can focus on what matters

Intezer security experts available on-demand
Your SOC. Zero constraints.
Your SOC.
Zero constraints.
Where human SOC teams review outcomes, not tickets


< 2% escalated for human review

Intezer security experts available on-demand

100% of alerts investigated at forensic depth

Detection rules automatically tuned
Sub-minute triage, 98% verdict accuracy
Fewer than 2% of alerts are escalated for human review so teams can focus on what matters
Security built on trust
Eliminates blind spots
Perfects detection posture
Strengthens detections with triage results informing rule creation and tuning, at the source, with ongoing tracking against the MITRE ATT&CK framework
Scales with your business needs
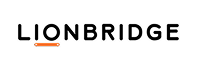
100+ Integrations
Connect your security products so you can triage and investigate all your alerts with Intezer’s AI SOC.


Orchestrate your SOC from a single intelligent platform
Free your team to focus on strategic security initiatives with AI SOC handling all the heavy lifting of alert triage. Contain threats in minutes, with human controlled or automated response.

Leave no alert behind
Intezer combines deep forensic capabilities, including endpoint analysis, memory scanning, reverse engineering, and built-in threat intelligence, with multiple AI models for fast, consistent, and accurate alert triage. Triage 100% of alerts with predictable endpoint-based pricing so even low-severity alerts are fully investigated.
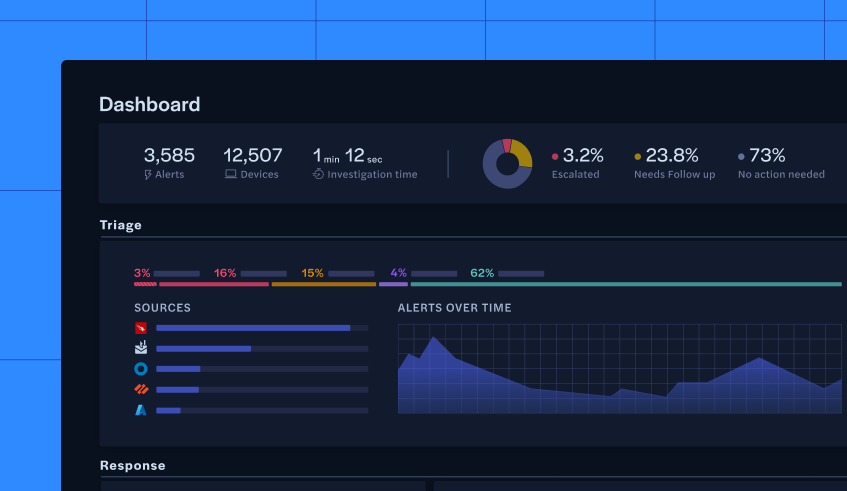
Reduce risk, not just noise
Intezer resolves over 98% of false positives in under a minute. Every alert is investigated at forensic depth with all outcome fed back into detection engineering. Noisy rules, broken detections and coverage gaps are all resolved. This transitions your SOC from managing alert volume, to systematically reducing hidden risk.
Customize triage and detections

Respond Automatically
Every escalated incident includes a tailored remediation plan that can be implemented in minutes, not hours or days. Actions such as disabling users or isolating devices can be triggered automatically via API or webhook, or reviewed and executed by analysts. Incidents can also be seamlessly routed to your SOAR or ticketing system for further handling.

Real stories. Real results.
Our customers tell our story better than we ever could. Here’s how Intezer has impacted their organizations.

We have a lean team, so automation is really critical to us. The amount of time that it takes to triage an event and understand what's really happening can eat into our ability to respond quickly. The more information that we have up front from Intezer when we get eyes on screen, the faster a human can make a decision about what to do. If we were to hire the amount of staff needed to respond at this scale, the cost could have been significantly higher too.

Michael Calderin
CISO
I've looked at a lot of security solutions over the years and the results from Intezer's Al-driven alert triage are actually amazing. Intezer integrates with all the modern security platforms, so teams have every alert fully investigated while enabling a fast time to respond. This technology is transformative for the efficiency and effectiveness of security operations.

Branden Newman
CTO
GMI is committed to continually advancing our Security Operations offering – leveraging an artificial intelligence capability is no longer a nice to have but a requirement to stay ahead. Our security operations ingest enormous amounts of data and Intezer is helping us by enhancing threat detection, automating responses, and reducing the workload on our security team. With Intezer, we can quickly identify and mitigate risks, reduce the 'noise,' and get our security teams focused on ensuring a more secure and resilient environment for our clients.

Jim Radzicki
President
We are thrilled to partner with Intezer and bring this powerful combination of technology and human intelligence to our clients. Our 24x7 SOC team, combined with Intezer's cutting-edge AI solution, offers an unmatched level of security and peace of mind for organizations of all sizes.

Mark Precious
CEO
Intezer has been a game-changer for our security operations. By automating tier 1 triage, we've drastically reduced alert fatigue and response times, allowing our team to focus on high-priority threats. Also, thanks to Microplus delivering Managed Security Service Provider services utilizing Intezer's Al-powered Autonomous SOC Platform, we've achieved a cohesive security ecosystem that is essential to our cybersecurity strategy.
Sandro Ramirez
Head of Security, Cotemar
In terms of IT security, Intezer definitely increases our efficiency. We are saving time. In terms of risk, we can react faster.

Piotr Albrecht
Security Officer
Intezer has transformed the way we handle tier 1 triage. By automating the initial investigation process, we've cut down on the noise from alerts, allowing our analysts to focus on real threats. The platform's accuracy and efficiency have not only improved our response times but have also given our team more bandwidth to tackle higher-level challenges. Intezer is now a cornerstone of our security operations.

Christian Hellemar
Head of Cybersecurity Services, tech stn.
Our partnership with Intezer allows us to leverage the power of AI to automate manual tasks and gain a deeper understanding of potential threats. By automating the triage of SIEM, EDR, and phishing alerts and providing us with enriched threat intelligence, Intezer empowers our security practitioners to focus on high-priority incidents and take decisive action to protect our clients’ business operations and reputation.

Todd Willoughby
Director
Ready to see for yourself?
See what Intezer’s AI SOC can do for your organization. Fill out the form to request a tailored demo and learn how to:
- Achieve 100% alert coverage and ensure no threat is missed across your business
- Accelerate investigations to reach clear, evidence-backed verdicts in under two minutes
- Enable your SOC to tackle today’s threat landscape without adding complexity